Mastering the Audit of Data Masking (Control 8.11) in ISO 27001:2022
Introduction: The Critical Role of Data Masking in Modern Compliance
 In the current era of digital transformation, data is often referred to as the new oil. However, unlike oil, data carries significant legal and ethical liabilities, especially when it concerns Personally Identifiable Information (PII).
In the current era of digital transformation, data is often referred to as the new oil. However, unlike oil, data carries significant legal and ethical liabilities, especially when it concerns Personally Identifiable Information (PII).
Under the ISO 27001:2022 framework, Control 8.11 (Data Masking) has emerged as a fundamental requirement for organizations aiming to limit the exposure of sensitive information.
When we look at the pillars of information security—the CIA triad, data masking primarily serves the “Confidentiality” pillar by ensuring that even if unauthorized users gain access to a database, the actual sensitive values remain obscured.
As an auditor or a business leader, understanding how to verify this control is vital for maintaining a robust Information Security Management System (ISMS).
Understanding ISO 27001:2022 Control 8.11
The transition from the 2013 version to the ISO 27001:2022 standard brought several new controls to the forefront, with data masking being one of the most impactful. The objective is simple: to limit the exposure of sensitive data to only those who strictly need to see it for their functional roles. This aligns perfectly with the “Principle of Least Privilege.”
For organizations seeking ISO 27001 Certification in Bangalore, auditors will expect to see a clear policy on how data is masked, particularly in non-production environments like development or testing. If your team lacks the technical depth to implement these nuances, engaging with seasoned ISO 27001 Consultants in Bangalore can bridge the gap between compliance requirements and technical execution.
Pre-Audit Phase: Determining the Scope of Masking
Before diving into the technical logs, an auditor must evaluate the “Data Masking Policy.” You cannot mask what you haven’t identified. The audit begins by reviewing the organization’s Data Classification Register.
The auditor will ask:
-
Has the organization identified which data elements require masking (e.g., Credit Card Numbers, PAN, Aadhaar, health records)?
-
Are the masking techniques appropriate for the risk level?
-
Is there a clear distinction between different types of controls in information security, such as preventive masking versus detective logging?
Expert ISMS consultants in Bangalore often suggest that a well-defined scope is the difference between a smooth audit and a major non-conformity (NC).
Auditing Technical Implementation: Static vs. Dynamic Masking
There are two primary methods of masking that an auditor will investigate: Static Data Masking (SDM) and Dynamic Data Masking (DDM).
-
Static Data Masking: This involves creating a copy of the database where sensitive data is replaced with “dummy” data. This is common in testing environments. An auditor will verify that the process is irreversible and that the original data cannot be reconstructed from the masked version.
-
Dynamic Data Masking: This happens in real-time. When a customer support agent views a profile, they might see
XXXX-XXXX-1234. The auditor will check the database permissions and the application layer logic to ensure the masking happens based on the user’s role.
Implementing these requires specialized knowledge. Many firms leverage ISO 27001 Implementation Services in Bangalore to ensure their SQL scripts or masking tools are configured correctly before the final certification audit.
Verifying Awareness and Competence
A control is only as strong as the people managing it. During an audit, it is common to interview developers and database administrators. If they aren’t aware of the masking policy, the control is effectively broken. This is where ISO 27001 awareness training in Bangalore becomes an invaluable asset.
An auditor will look for:
-
Training logs showing that staff understand the risks of data leakage.
-
Evidence that the “Right to be Forgotten” or “Data Minimization” principles are being upheld via masking.
-
Knowledge of how to handle “unmasking” requests in emergency scenarios.
Common Audit Pitfalls to Avoid
As a consultant, I often see organizations fail their data masking audits for the following reasons:
-
The “Masking the Mask” Error: Using weak algorithms that allow “re-identification” via inference.
-
Neglecting Backups: Masking the live database but leaving sensitive data in unencrypted, unmasked backups.
-
Inconsistent Rules: Masking the “Email” field in the CRM but leaving it visible in the Finance module for the same user level.
To avoid these, it is recommended to conduct internal audits or gap analyses. Utilizing professional ISO 27001 Consultants in Bangalore helps identify these blind spots before the external certification body arrives.
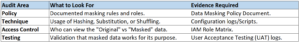
The Audit Checklist for Control 8.11
When preparing for your ISO 27001 Certification in Bangalore, use this condensed checklist:
Conclusion: Securing Your Competitive Advantage
Auditing data masking is not just a checkbox exercise; it is a strategic move to build trust with your clients and stakeholders. By effectively obscuring sensitive information, you mitigate the risk of massive fines and reputational damage.
Whether you are just starting your journey or looking to refine your existing systems, seeking expert ISO 27001 Implementation Services in Bangalore ensures that your technical controls are both compliant and efficient. Don’t leave your data security to chance—ensure your team is equipped with the right ISO 27001 awareness training in Bangalore to maintain these standards year-round.